The Sovereign Trust Layer
A New Chapter for Digital Sovereignty in Europe

_____________________________________________________________________________________________________________________
Author: Rami Cherri | Pioneer of Institutional Trust Infrastructure Date: January 2026 Classification: Strategic Position Paper
________________________________________________________________________
Table of Contents
1. Introduction: The Invisible Border in Digital Space
2. Part I: The Dilemma - When Laws Collide
3. Part II: Why Politics Cannot Solve the Problem
4. Part III: The Architectural Answer
5. Part IV: AI Governance in the Age of the EU AI Act
6. Part V: The Market for Sovereignty
7. Part VI: The Hurdles for European Innovators
8. Part VII: The Path Forward
9. Appendix: Architecture Overview
________________________________________________________________________
1. Introduction: The Invisible Border in Digital Space
Imagine you operate a bank in Frankfurt. Your customer data—account balances, transaction histories, personal information of millions of people—lies securely encrypted in the cloud. But one morning you receive a letter: An American authority demands access to this data. Not through German courts. Not through European institutions. Directly. And your cloud provider, a US company, is legally obligated to cooperate .
This is not a hypothetical dystopia. It is the legal reality of the CLOUD Act of 2018.
While Europe has built the world's strictest data protection laws over the past years—from GDPR to DORA to the EU AI Act—there exists in parallel an extraterritorial reach of American laws that can technically circumvent these achievements. The question is no longer whether this problem must be solved, but how .
The answer, argues a growing movement of technologists, lawyers, and entrepreneurs, lies not in political negotiations or diplomatic declarations of intent. It lies in the architecture itself .
________________________________________________________________________________________________________________________
2. Part I: The Dilemma – When Laws Collide
The GDPR: Europe's Digital Shield When the General Data Protection Regulation came into force on May 25, 2018, it was more than just a regulation. It was a statement: Europe would chart its own course on the question of who owns personal data and who may dispose of it. The answer was unequivocal: the individual .
The GDPR established principles that are now considered the gold standard worldwide:
- Purpose Limitation: Data may only be used for the purpose for which it was collected.
- Data Minimization: Only the most necessary information may be gathered.
- Storage Limitation: Data must be deleted as soon as it is no longer needed.
- Integrity and Confidentiality: Technical measures must ensure protection .
But perhaps the most important provision is found in Article 48: The transfer of personal data to third countries based on judgments or decisions of foreign authorities is only permissible if based on an international agreement. Without such an agreement, disclosure is simply illegal .
The CLOUD Act: America's Long Arm
In the same year, just two months before the GDPR took effect, President Trump signed the Clarifying Lawful Overseas Use of Data Act—better known as the CLOUD Act. The law was a response to a protracted legal dispute between Microsoft and the FBI over email data stored on servers in Ireland .
The core message of the CLOUD Act is remarkably simple: If a company is headquartered in the USA or conducts substantial business there, it is subject to American jurisdiction. Regardless of where in the world the data is physically stored .
For US authorities—from the FBI to the SEC to intelligence agencies—this means: A court order from Virginia can compel the surrender of data located in Frankfurt, Amsterdam, or Dublin.
________________________________________________________________________________________________________________________
3. Part II: Why Politics Cannot Solve the Problem
The Trans-Atlantic Data Privacy Framework: A Fragile Compromise In 2022, the USA and the EU ceremoniously announced a new agreement: the Trans-Atlantic Data Privacy Framework (TADPF). It was supposed to end the legal uncertainty after Schrems II and create a stable framework for data transfers .
But experts were skeptical from the start. The agreement was essentially based on an Executive Order from President Biden that provided certain restrictions on intelligence activities. The problem: An Executive Order can be revoked by a subsequent president with the stroke of a pen. It is not law. It is a promise .
Max Schrems immediately announced he would challenge this agreement before the ECJ as well. Schrems III is not a question of "if" but "when." And this time, the ruling could be even more far-reaching: Should the ECJ also strike down the TADPF, Europe would stand without any legal basis for transatlantic data transfers .
The Structural Impossibility of a Political Solution The real problem runs deeper than negotiating skill or political will. It lies in the fundamental incompatibility of two legal systems .
The GDPR is based on the concept that data protection is a fundamental right enshrined in Article 8 of the EU Charter of Fundamental Rights. It is non-negotiable. It cannot be weighed against economic interests. It is absolute .
The American legal system knows no such fundamental right. Data protection in the USA is a patchwork of industry regulations and contractual agreements. And where national security comes into play, intelligence agencies traditionally have far-reaching powers .
These two worldviews cannot be harmonized through an agreement. You cannot guarantee a fundamental right through an Executive Order.
_____________________________________________________________________________________________________________________
4. Part III: The Architectural Answer
From Politics to Physics If political solutions are structurally impossible, only one path remains: Technology must accomplish what law cannot.
The core idea is compellingly simple: If data is encrypted such that no one—not the cloud provider, not authorities, not hackers—can read it, then it becomes irrelevant which laws apply in which country. A judge in Virginia can order the surrender of data. But if that data is merely an unreadable jumble of characters for the cloud provider itself, the order comes to nothing .
This is not theoretical speculation. It is the principle of customer-managed encryption—and it forms the heart of what is called the Sovereign Trust Layer.
The Split-Key Architecture: Whoever Holds the Key Holds the Power In traditional cloud architectures, encryption works roughly like this: The cloud provider encrypts your data with a key that it generates and manages itself. This is better than no encryption but it does not protect against the provider itself or against authorities that can compel its cooperation .
The split-key architecture turns this model on its head. The master key is not generated by the cloud provider, but by the customer—and it never leaves the customer's sovereign domain.
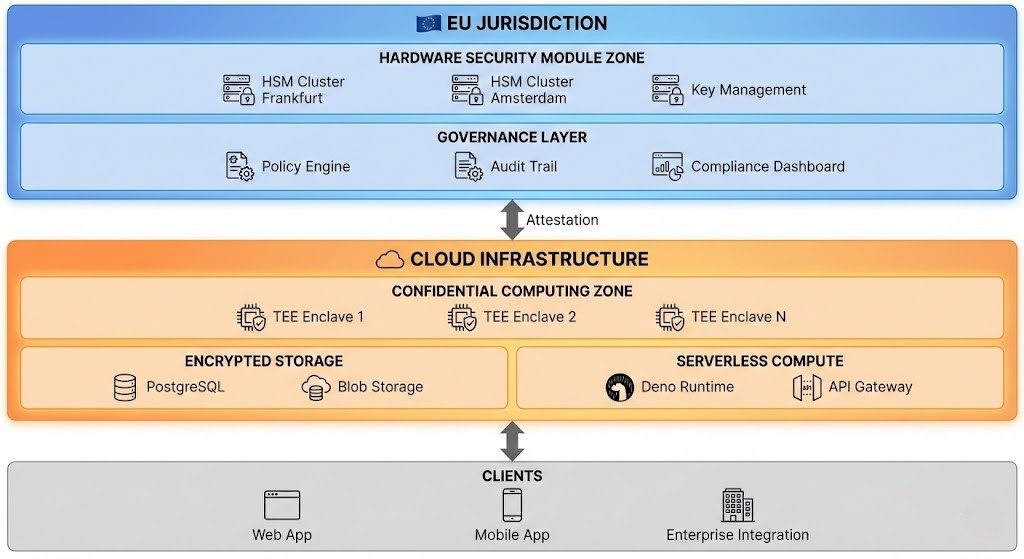
This is technically realized through Hardware Security Modules (HSMs)—specialized, tamper-resistant devices that perform cryptographic operations and store keys. The crucial point: These HSMs are located in EU data centers, operated by EU companies, and subject exclusively to EU law .
When a US authority now demands data from Microsoft, Google, or Amazon, these companies can only deliver encrypted data packets. The keys to decrypt these packets are not within their access. They lie in an HSM in Frankfurt or Amsterdam and thus beyond the reach of the CLOUD Act .
Figure 1 - Split-Key Architecture
Confidential Computing: When Even Memory Is Blind
But encryption alone is not enough. Data must be processed—and in the moment it is decrypted for processing, it is theoretically vulnerable. Even if only for milliseconds .
This is where Confidential Computing comes in—a technology developed in recent years by Intel (SGX), AMD (SEV), and Arm (TrustZone) and now available in cloud environments like Azure Confidential Computing.
The basic principle: An isolated area of the processor—a so-called Trusted Execution Environment (TEE) or enclave—processes data in a state that is invisible even to the operating system, the hypervisor, and the cloud administrator. The data remains encrypted throughout processing—not just at rest (stored) and in transit (transmitted), but also in use (during processing) .
For an attacker—whether a hacker, a dishonest administrator, or an authority with a court order—the contents of the enclave are inaccessible. What they see is a black box that receives inputs and produces outputs. What happens in between remains invisible .
________________________________________________________________________________________________________________________
5. Part IV: AI Governance in the Age of the EU AI Act
The Problem with "Intelligent" Systems The previous discussion may sound plausible for traditional data processing. But what happens when we introduce Artificial Intelligence into the equation? .
AI systems—particularly generative models like GPT-4 or Claude—are not deterministic programs. They are probabilistic. This means: Even with identical inputs, they can produce different outputs. Their behavior is not fully predictable .
This raises a fundamental problem for data protection and compliance. Traditional security controls are based on rules: "If request X, then action Y." But an AI system based on a Large Language Model follows no explicit rules. It generates responses based on statistical patterns in training data .
What does this mean for the protection of personal data? Suppose a company deploys an AI assistant that can access customer data. A system prompt says: "Never reveal personal data." Is that a guarantee? The honest answer: No .
System prompts are suggestions to an AI model, not laws. Under certain conditions—adversarial prompts, jailbreaks, unusual contexts—these instructions can be circumvented .
The EU AI Act: From Guidelines to Obligations In August 2025, the EU AI Act will be fully enforced for high-risk AI systems. This law—the world's first comprehensive AI regulation—requires, among other things:
- Transparency: Users must know they are interacting with an AI.
- Robustness: Systems must be protected against manipulation.
- Data Governance: Training data must be documented and audited.
- Human Oversight: Critical decisions must be supervisable by humans.
- Auditability: Companies must be able to demonstrate that their systems are compliant .
The last point is the crucial one and the most difficult. How do you prove that a probabilistic system, whose internal behavior is not fully understandable even to its developers, follows the rules? .
Paper Compliance vs. Architectural Containment The traditional answer from the compliance industry is: Documentation, audits, policies. You write down what the system should do, conduct periodic tests, and hope for the best .
This approach—let's call it "Paper Compliance"—works tolerably well for deterministic systems. For AI, it is doomed to fail. Why? Because billions of interactions can occur between one audit and the next. Because adversarial actors are creative and develop new attack vectors. Because models are updated, prompts are changed, data sources evolve. Paper Compliance is a photograph; AI systems are a movie .
The alternative is what is called architectural containment: Instead of validating that a system behaves correctly, you ensure that it cannot behave otherwise.
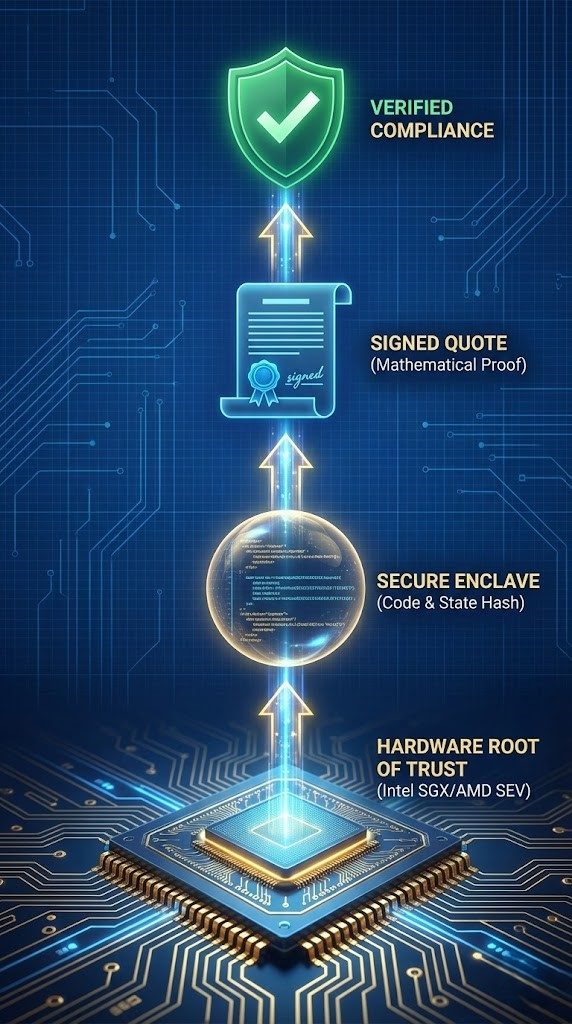
Cryptographic Attestation: Trust as Mathematical Proof In a traditional environment, trust is based on logs: Protocol files that record what happened when. The problem: Logs can be manipulated. An administrator with access can delete, alter, or forge entries .
Cryptographic attestation works differently. The hardware itself—the processor with its TEE—generates a signed report (a so-called "Quote") that mathematically proves:
What code is running: A hash of the executed program is embedded in the quote.
In what state: The configuration of the enclave is part of the signature.
That nothing was manipulated: Any change would alter the hash and invalidate the quote .
This mechanism is not triggered periodically but continuously. It is not a sample; it is an unbroken chain of proofs.
________________________________________________________________________________________________________________________
6. Part V: The Market for Sovereignty
A €50 Billion Ecosystem Digital sovereignty is not just a political buzzword. It is a market—and a massive one. European companies spend an estimated €100 billion annually on cloud services. A substantial portion of this flows to US providers. Given the regulatory uncertainty—Schrems III, CLOUD Act, EU AI Act—the willingness to pay for demonstrable sovereignty is considerable .
Analysts estimate the addressable market for sovereign cloud infrastructures in Europe at €50 billion—and growing.
Who Are the Customers? Demand comes from various sectors:
FINANCIAL SERVICES: Banks and insurers are subject not only to GDPR but also to the Digital Operational Resilience Act (DORA), which from January 2025 imposes strict requirements on IT resilience and outsourcing risks.
HEALTHCARE: Patient data is the most sensitive of all data assets. The combination of GDPR, national health data protection laws, and the growing use of AI for diagnostics creates enormous demand .
PUBLIC SECTOR: Authorities, ministries, critical infrastructures—wherever state sovereignty meets digital processes, the question of data control is existential.
CRITICAL INFRASTRUCTURES: Energy suppliers, telecommunications companies, transport operators—the NIS2 Directive obligates these sectors from October 2024 to enhanced security measures.
The Hyperscalers' Perspective It would be a misunderstanding to see Microsoft, Google, and Amazon as opponents of digital sovereignty. On the contrary: These companies have a vital interest in retaining the European market .
Microsoft has taken steps in this direction with Azure Confidential Computing and partnerships with European providers. Google promotes its "Sovereign Cloud" offering. AWS has expanded European data center zones .
But all these offerings have a common problem: As long as the US parent company ultimately has access to the keys—or could have—the CLOUD Act risk remains.
A Sovereign Trust Layer as an independent, EU-jurisdictioned intermediate layer could be the solution all sides need.
________________________________________________________________________________________________________________________
7. Part VI: The Hurdles for European Innovators
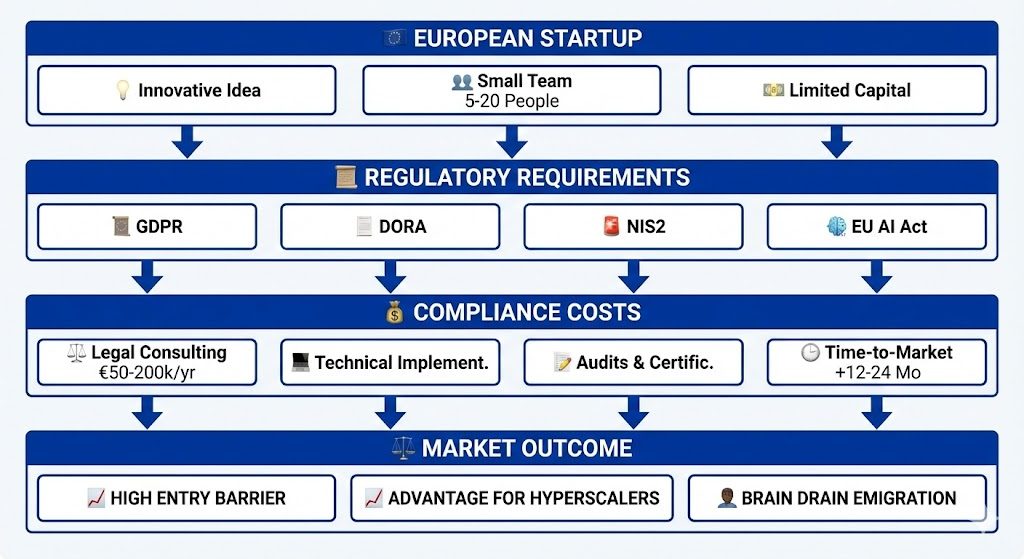
The Paradox of Regulation: Protection as Barrier Europe's regulatory framework—GDPR, DORA, NIS2, EU AI Act—was created to protect citizens and businesses. But for European startups and innovators, this protection has a paradoxical effect: It becomes a market entry barrier .
Compliance costs are substantial. A fintech startup developing an AI-based credit assessment must not only build a functioning product. It must also:
Conduct a Data Protection Impact Assessment under GDPR
Implement a risk management framework under DORA
Document a conformity assessment under EU AI Act
Demonstrate technical measures for NIS2 compliance .
For a company with five engineers and limited capital, this is a Herculean task.
Competitive Distortion Favoring Established Players The irony: The same regulations meant to strengthen European sovereignty often favor the US hyperscalers they address. Why? Because Microsoft, Google, and Amazon have the resources to maintain compliance teams, obtain certifications, and adapt their infrastructure accordingly .
A European startup wanting to develop a sovereign alternative must overcome these hurdles with a fraction of the resources. The result is a regulatory moat: Established providers are protected by the complexity that deters newcomers .
The Danger of Brain Drain A complex regulatory environment has consequences that extend beyond individual companies. Talent—the developers, researchers, and entrepreneurs who drive innovation—is mobile. If Europe is perceived as too bureaucratic, too slow, too risk-averse, they leave .
According to a study by the European Investment Fund, European entrepreneurs who want to build a successful tech company are highly likely to found it in the USA—not because of a lack of talent in Europe, but because of the more favorable regulatory and financing climate.
Strategies to Overcome the Hurdles Despite these challenges, there are ways European innovators can succeed:
LEVERAGE COMPLIANCE-AS-A-SERVICE: Instead of building their own compliance teams, startups can rely on specialized service providers. The Sovereign Trust Layer itself is an example: An infrastructure that delivers GDPR, DORA, and EU AI Act compliance "out of the box" .
PARTNERSHIPS WITH ESTABLISHED PROVIDERS: European startups can cooperate with cloud providers that already have compliance frameworks. The downside: This reinforces dependence on US providers .
USE REGULATORY SANDBOXES: Several EU countries have established regulatory sandboxes where innovative companies can test under relaxed conditions.
POSITION SOVEREIGNTY AS COMPETITIVE ADVANTAGE: In a market increasingly sensitized to data protection, demonstrable compliance can become a differentiating feature.
The Role of the Sovereign Trust Layer as Enabler The Sovereign Trust Layer is not just a solution for large companies' CLOUD Act problem. It is a platform that enables European innovators to access the market:
- Pre-configured Compliance: Startups inherit the platform's certifications.
- Cost Sharing: Infrastructure costs are distributed across many users.
- Trust Signal: Usage signals security to customers and investors.
- Faster Time-to-Market: Developers can focus on their product .
________________________________________________________________________________________________________________________
8. Part VII: The Path Forward
From Technology to Standard Technically, the problem is solvable—the building blocks exist:
Hardware Security Modules are market-ready.
Trusted Execution Environments are available in modern processors.
Client-side encryption is a solved problem.
Cryptographic attestation works .
What is missing is institutional recognition—the official confirmation by EU authorities that this architecture meets the requirements.
Specifically, three steps are needed:
RECOGNITION AS "SUPPLEMENTARY MEASURE" UNDER SCHREMS II:
The ECJ has clarified that data transfers to third countries can be secured with additional technical measures. Customer-managed encryption with EU-jurisdictioned keys should be officially recognized as such .
INTEGRATION INTO EU CLOUD SECURITY STANDARDS: The requirements for the EU Cybersecurity Certification Scheme for Cloud Services (EUCS) should adopt this architecture as a reference model.
CLARIFICATION OF THE CLOUD ACT COLLISION: A formal opinion from the European Data Protection Board (EDPB) would create enormous legal certainty.
A Call to Action Time is pressing. Schrems III is on the horizon. The EU AI Act is taking effect. DORA deadlines are approaching. Companies need clarity now .
The Sovereign Trust Layer offers a solution that is technically sound, legally defensible, and economically viable. What is missing is the political will to elevate it to a standard .
TO THE EU COMMISSION: Recognize architectural sovereignty as a supplementary measure.
TO DATA PROTECTION AUTHORITIES: Create clarity on the technical conditions under which CLOUD Act risks are considered mitigated.
TO THE HYPERSCALERS: Support European sovereignty solutions as partners, not competitors.
TO EUROPEAN INNOVATORS: Use sovereign infrastructures to position compliance as a competitive advantage .
The Future of Europe's Digital Sovereignty The future of Europe's digital sovereignty will not be decided in negotiation rooms. It will be built in data centers, written in code, and cast in hardware. It is time to start building .
________________________________________________________________________________________________________________________
9. Appendix: Architecture Overview
Complete Architecture of the Sovereign Trust Layer
© 2026 immo.quick Global — Rami Cherri | Pioneer of Institutional Trust Infrastructure